What is a 51% Attack on the Blockchain?
Salomon Kisters
Dec 28, 2022This post may contain affiliate links. If you use these links to buy something we may earn a commission. Thanks!
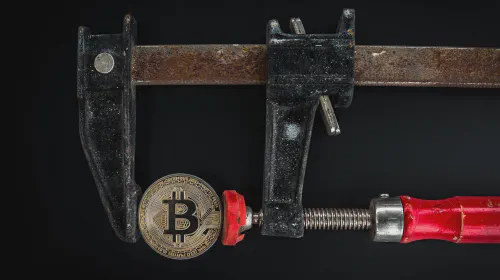
A 51% attack refers to an attack on a blockchain network in which an attacker or group of attackers control more than 50% of the network’s mining power, also known as the “hash rate.”
Since everything on the blockchain is decided through consensus, 51% control over the network allows people to do pretty much anything they want. This completely destroys the blockchain’s ability to protect itself and leaves it at the mercy of the controlling party. There have been cases in history where blockchains have been almost completely wiped out because of such loss of control.
In a time where digitization is everything and many industries are rapidly shifting towards bleeding-edge technology, the adoption rate of the blockchain is also on the rise. However, most people are not yet comfortable with the rapid adoption of new technologies and are still sitting on the fence.
If you are about to invest in cryptocurrency, use the blockchain for a project, or do anything else that involves blockchain technology, you should know what a 51% attack is, and how you can prevent a 51% attack from happening.
What is Blockchain?
To better understand the 51% attack, we need to go back to the basics. A blockchain is a decentralized, digital ledger of transactions that uses cryptography to record and verify transactions. It is called a “chain” because it consists of a series of blocks that are linked together and secured using cryptography. Each block contains a record of multiple transactions, and once a block is added to the chain, the transactions it contains are considered to be permanently recorded and verified.
One of the key features of a blockchain is that it is decentralized, meaning that it is not controlled by any single entity or organization. Instead, it relies on a network of computers, known as nodes, to validate and record transactions. This decentralized structure makes it difficult for any single entity to alter or tamper with the information recorded on the blockchain, making it a secure and transparent system to store and transmit data.
Blockchains have many potential uses, including enabling the creation of new digital currencies, such as Bitcoin, and allowing the secure and efficient transfer of assets and information without the need for intermediaries. They are also being explored for use in a wide range of industries, including finance, supply chain management, and voting systems.
How are 51% of Attacks Executed?
As already mentioned, a 51% attack is a type of attack when a single entity or group of entities controls more than 50% of a blockchain’s computing power. This allows them to manipulate the blockchain and double-spend coins, as well as prevent new transactions from being confirmed.
There is no limit to what hackers can do with this level of control. The attacker or group of attackers can engage in various malicious activities.
Double Spending
This refers to the ability to spend the same cryptocurrency more than once. An attacker with 51% control could potentially create a transaction, wait for it to be included in a block, and then use their control to create a new block that does not include the transaction. This means that the attacker will keep the cryptocurrency they already spent, while still maintaining control of it.
Reversing Transactions
With 51% control, an attacker could potentially reverse transactions that have already been confirmed by the network. This could then be used to cancel legitimate transactions or to facilitate fraudulent activity.
Block Censorship
An attacker with 51% control could also potentially censor new blocks from being added to the chain, allowing them to selectively exclude transactions from being processed.
Overall, a 51% attack can have serious consequences for the overall security and integrity of a blockchain network, and it is generally considered a major threat to the decentralized nature of blockchain technology.
PoW vs. PoS
A 51% attack is generally more difficult to execute on a Proof-of-Stake (PoS) blockchain as compared to a Proof-of-Work (PoW) blockchain. Let us explain to you why that is the case.
In a PoW blockchain, miners compete to solve complex mathematical problems to validate transactions and create new blocks. The miner who successfully solves the problem first gets to add the new block to the chain and is rewarded with a certain amount of cryptocurrency.
Because the ability to add new blocks is directly tied to the ability to solve these mathematical problems, an attacker with 51% control of the mining power (hash rate) would be able to execute a 51% attack by controlling the majority of the mining power and using it to add malicious blocks to the chain.
In a PoS blockchain, for instance, the process for validating transactions and adding new blocks is different. Instead of mining, validators (often called “stakers”) are chosen to create new blocks based on the amount of cryptocurrency they hold and are willing to “stake” (i.e., lock up) as collateral.
The probability of being chosen as a validator is proportional to the amount of cryptocurrency staked. Because it is more challenging for an attacker to acquire the large majority of the staked cryptocurrency compared to most of the mining power in a PoW blockchain, it is generally considered more difficult to execute a 51% attack on a PoS blockchain.
That being said, it is still possible for an attacker to execute a 51% attack on a PoS blockchain, although it would require a much larger investment in terms of the amount of cryptocurrency that would need to be acquired and staked. As a result, PoS blockchains are generally considered to be more secure against 51% of attacks.
Some Well-Known 51% Attacks
The Grin blockchain experienced a 51% attack in which an unknown miner gained control of over 57% of the total hash power. The attack prompted Grin to stop payouts and advise miners to halt operations until the issue was resolved. The blockchain eventually regained control and implemented better security measures to prevent such attacks in the future.
Similarly, Vertcoin also had the same ill luck. In fact, the Vertcoin blockchain has experienced multiple 51% attacks in the past, resulting in genuine blocks being replaced by attacker-written blocks and causing double spending and significant losses for investors. Vertcoin had to switch to a more powerful Proof-of-Work (PoW) algorithm and block powerful mining chips from the network to improve security.
The Bitcoin Gold (BTG) blockchain experienced two 51% attacks, one in 2018 and one in 2020, resulting in double spending and significant losses for users. The BTG community called for the development and implementation of a more secure algorithm to prevent future attacks. The Ethereum Classic (ETC) blockchain, too, faced three consecutive 51% attacks in the same month in 2020. Millions of dollars were lost and the reputation of the blockchain was tarnished since safety is considered one of the key features of a blockchain.
These are just a few examples of 51% of attacks that have occurred on blockchains so far. It is important to note that while 51% of attacks can have significant consequences, they are relatively rare and most blockchains have robust security measures in place to prevent them from occurring.
How to Check if a Blockchain is Vulnerable
Before using a blockchain for investment or transaction purposes, it is important that you carefully research and determine if it’s a safe option. There are a few ways to check if a blockchain is vulnerable to 51% of attacks, which are discussed next.
Check the Mining Power Distribution
One way to assess the vulnerability of a blockchain to 51% attacks is to look at the distribution of its mining power (also known as “hash rate”) among the miners on the network. If a small number of miners control a significant portion of the mining power, it may be easier for them to execute a 51% attack.
Check the Network Size
Another factor to consider is the size of the network. In general, larger networks with more miners and more distributed mining power are less susceptible to 51% attacks as compared to smaller networks.
Check the Blockchain’s Consensus Algorithm
The type of consensus algorithm used by a blockchain can also impact its vulnerability to 51% attacks. For example, Proof-of-Work (PoW) consensus algorithms, which are used by many blockchains including Bitcoin and Litecoin, are more vulnerable to 51% attacks compared to Proof-of-Stake (PoS) algorithms, which are used by some newer blockchains.
Monitor the Blockchain for Unusual Activity
It is also possible to monitor the blockchain for unusual activity that may point to a 51% attack in progress, such as a sudden increase in the number of blocks being produced by a single miner or a high number of transactions being reversed.
Overall, it is important to keep in mind that no blockchain is completely immune to 51% of attacks, but some are more vulnerable than others. It is always a good idea to be aware of the security measures in place on any blockchain and to take steps to protect your assets if you are concerned about the possibility of a 51% attack.
Stay informed with the latest insights in Crypto, Blockchain, and Cyber-Security! Subscribe to our newsletter now to receive exclusive updates, expert analyses, and current developments directly to your inbox. Don't miss the opportunity to expand your knowledge and stay up-to-date.
Love what you're reading? Subscribe for top stories in Crypto, Blockchain, and Cyber-Security. Stay informed with exclusive updates.
Please note that the Content may have been generated with the Help of AI. The editorial content of OriginStamp AG does not constitute a recommendation for investment or purchase advice. In principle, an investment can also lead to a total loss. Therefore, please seek advice before making an investment decision.
Can The Blockchain Be Hacked Or Attacked?
Blockchain technology and cryptocurrencies have seen a massive surge in popularity. Can they be hacked?

Which Factors Make the Blockchain Secure?
The blockchain is secure under certain conditions and cannot be manipulated. Which factors contribute to the security of an existing blockchain? Read more here.

Immutability in Blockchain: Ensuring Data Integrity and Boosting Trust
Immutability is a core defining feature of the Blockchain that ensures data integrity, boosts trust, and simplifies auditing processes for businesses.
Protect your documents
Your gateway to unforgeable data. Imprint the authenticity of your information with our blockchain timestamp