What Is Blockchain-Based Timestamping and Who Needs It?
Salomon Kisters
Oct 26, 2020This post may contain affiliate links. If you use these links to buy something we may earn a commission. Thanks!
The old world of centralized systems and their business models relied heavily on the idea of trust. For every transaction, document, and signature, the end-user had to hope that the received data is real and not manipulated or edited. As industries move more and more towards full digitalization, it becomes increasingly important to develop a system that replaces the need for trust. For some, blockchain-based timestamping might be the only solution to this problem.
 Source: financeonline.com
Source: financeonline.com
With the help of blockchain technology, we have access to an immutable, anonymous, and decentralized public ledger where all information is cryptographically recorded. Today, blockchain networks offer a viable solution for keeping track of data and verifying its authenticity, which businesses and users can adopt to once and for all let go of trust-based systems.
In this article, we will dive deeper into blockchain technology and explain how you can use blockchain-based timestamping to verify that a document existed at a particular date and time. Furthermore, we will also provide you with insight on how to safely and easily utilize this method with the help of OriginStamp.
What is a blockchain network?
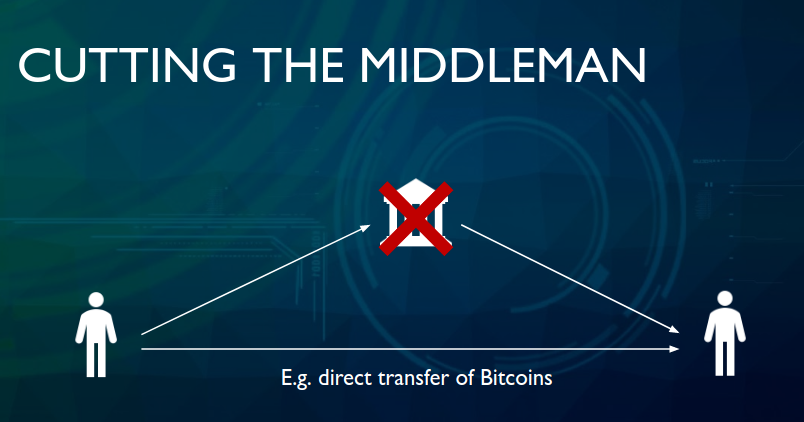
The easiest way to understand blockchain technology is to view it as a public ledger where every single transaction is permanently recorded and cannot be deleted or edited. Users have the ability to anonymously create transactions that transfer either data (in the form of messages) or money. These networks are decentralized and hence remove any need for a central authority that guards and manages the ledger. Moreover, it is also distributed to the point that every participant has a transparent and full copy of the ledger.
The Bitcoin whitepaper
The first blockchain network arrived consequently with the creation of Bitcoin. The anonymous creator Satoshi Nakamoto published a whitepaper called Bitcoin: a Peer-to-Peer Electronic Cash System in which he described the mechanisms implemented in this decentralized, distributed, anonymous, and immutable technology.
In the context of verifying the authenticity and creation of data, Nakamoto developed timestamps based on the use of hash-based proof of work. In this network, a Timestamp Server takes the hash of a block containing transactions to be timestamped and published on the network. By doing so, the server ensures that the transactions have existed at this point in time. This system is chronologically enforced as each transaction hash contains the timestamp of the previous block of transactions, forming a chain of blocks.
These blocks are created, moved, and verified with the help of miners in a Proof-of-Work consensus model (Ethereum.org). The miner is financially incentivized by the network to verify these blocks of transactions by solving complex mathematical problems. They make the backbone of the technology, in this specific model, and essentially keep the network moving. By working together, miners reach a consensus on the state of the ledger and the authenticity of its records. Via this system, we can know for certain not only the data of a record’s timestamp but that no one can manipulate it as well.
The first implementations of trusted timestamping
Timestamping is not an idea that appeared in the 21st century for the first time. In fact, people have historically searched for ways to securely track and authenticate documents. Post stamps are viewed to be the precursor and first utilization of timestamping but in a very crude way.
The first ‘real’ time people tried to claim ownership over documents was in the 17th century. A number of scientists attempted to patent or prove ownership over their innovative findings by sending letters to themselves. For example, Robert Hooke published an anagram in 1660 as proof of his discovery of Hooke’s Law.
“Hooke first announced his law of elasticity as an anagram. This was a method sometimes used by scientists, such as Hooke, Huygens, Galileo, and others, to establish priority for a discovery without revealing details.” wikipedia.org
More than ten years later, famous scientist Isaac Newton similarly sought to protect his ideas through telegrams. In a letter to Leibniz in 1677 where he explained his ‘Fluxional Technique,’ the scientist concealed his discovery by encrypting it.
Centralized infrastructures for timestamping
With the arrival of computers, we had the chance to see one of the first real implementations of timestamping. However, none of these methods were secure enough. A major problem was that they required a centralized infrastructure. These systems inherently lead to data manipulation in spite of using complex methods for encrypting timestamps. The only way to solve this problem was through decentralization, and blockchain networks are the only practical implementation of decentralized timestamping so far.
Introduction of Blockchain
Blockchain technology has the potential to completely replace traditional public notaries, which are far too inefficient to process large amounts of information. Their digital versions appeared for the first time in the early 1990s in the form of e-notaries. However, neither an e-notary nor modern public notaries have the properties that could make data authorization, procurement, and processing safe or cost-efficient.
For now, we have to rely on blockchain networks. However, we may even live to see new technologies that surpass the capabilities of today’s decentralized solutions. In the case that we better understand how encryption works, scientists may create quantum-resistant encryption protocols that would mark the end of this discussion. Encryption would finally reach a sufficient level and we would only have to decide whether centralized or decentralized hierarchies would manage our data.
But to get back to reality, we will further discuss the importance of timestamping and how it can be done via blockchain technology. In the next section, we will take an in-depth look at which industries and sectors can benefit from this way of securing and tracking data. We will provide an overview of multiple use cases. These include financial, social, governance, and informational examples.
Who needs blockchain-based timestamping?
With the previous brief explanation of how decentralized networks work, we can conclude that blockchain-based timestamping is a completely secure way of tracking the creation and modification time of a document. More so, it is secure enough that even the owner of a document does not have the power to change any data once a document has been recorded.
Since the creation of Bitcoin in 2009, both blockchain technology and the world have come a long way. Today’s society is more digitalized than it ever was in the history of mankind. But for technology to spur in a healthy way, we need the widespread adoption of a system that removes trust and thus prevents any kind of malicious activity.
The value and use cases for this kind of decentralized and immutable timestamping are limitless. In fact, the adoption of blockchain-based timestamping can already be seen across multiple sectors and industries worldwide. It can be used for governance, trading, payments, insurance, supply chains, and much more.
Financial Use Cases
As we see with Bitcoin, the very first use case for blockchain technology was sending financial value and information through transactions. There are hundreds of cryptocurrencies and blockchain networks that facilitate payments in a trustless, decentralized, and cost-effective way.
Why have a bank account when you can be your own bank? And why send a wire transfer when you can make a payment in only a few minutes? Apart from creating digital transactions, you can also verify them and show proof of ownership through blockchain-based timestamping. In the next section, we will show you how blockchain is used for crypto payments, cross-border payments, and insurance.
Cryptocurrencies
Of course, decentralized timestamping had its first real use cases with the emergence of cryptocurrencies. As previously explained, blockchain-based timestamping originally came with the creation of Bitcoin. Its blockchain network made it possible to create timestamps for every transaction within the ledger. This enables a sort of Proof of Existence where we know exactly at what point a transaction was created and what it contained.
For example, if Person A made a cryptocurrency payment to Person B, who claims that he received no money, the sender could theoretically use the blockchain network’s public information in court. Since the network is basically an immutable ledger where all participants reached a consensus on its ongoing state, we have a situation where the payment is practically certified by the entire network.
Since we already explained how a blockchain network works, who its participants are, and how transactions are verified, we will move to more real world-based financial use cases in finance.
Cross-Border payment systems
Reports indicate that the global remittance market was valued at $682.6 billion in 2018. By 2026, it is projected to grow up to $930 billion. In recent years, cross-border payment companies have expressed their interest in adopting blockchain technology to provide faster interbank payments. For example, the largest global banking ecosystem SWIFT plans to use blockchain technology to provide 24-hour payment and clearing capabilities.
With cryptographically-encrypted timestamps, blockchain technology solves the issue of double-spending, where a user spends the same assets more than once. Therefore, it is possible to use decentralized technology to support faster and more cost-efficient global payments. Moreover, blockchain could also help with battling money laundering.
Insurance Claims
Insurance claims represent another important financial use case. Blockchain technology enables a more transparent and fraud-free insurance system. Any insurance company can create its own public or private blockchain network to store data regarding insurance claims as the information is permanently recorded and immutable. Moreover, there is no way to manipulate or edit the information once it is written.
By using a decentralized system insurance companies would save a lot of time and money. Due to the inherent features of blockchains, it would only take one simple request for an entity to check whether an individual paid his insurance or if he even has it. This would also improve the experience of customers as they could track their payments and insurance status all in one place, without using an intermediary.
Goods, products, and services
In a globalized world where trading, services, and people are interconnected, it is necessary to keep track of what we transfer and consume, be it physically or digitally. The sole reason why black markets and grey markets exist today is that the goods we produce cannot be tracked. We do not know where our food comes from. We do not know if the medicine we use came from a real certified laboratory or not. We do not even know if our documents are validly certified by a real regulatory body or administration.
All of these problems stem from failing to authenticate and track the flow of goods and services. Mainly, the problem starts with supply chains as they represent the first ‘point of attack’ where a product could be maliciously misrepresented. In this segment, we can see how blockchain technology assists companies and users with its inherent function of tracking ownership and data flow.
Supply Chains
Another fascinating use case for blockchain-based timestamping can be found in modern supply chains. In this case, we can track the price, location, quality, certification, delivery date, and all kinds of other information regarding goods. Blockchain supports the creation of a transparent and traceable supply chain that lowers losses, counterfeit products while improving compliance and visibility. In fact, supply chains represent the biggest use case for decentralized technology.
From the moment a product is processed or developed to the day it is delivered, we can track every single step in the production line. This is especially important as using blockchain networks reduces administrative costs and the paperwork needed to physically track and record this data. Furthermore, it improves visibility and compliance, removing any need for outsourced contract manufacturing. Again, the transparent aspect of blockchain technology minimizes the market share counterfeit products and gray market trading have.
Another set of improvements is that the credibility and public trust of a product line can be increased. The same applies for reducing public relation endangerment in the case of malicious activity.
In practice, blockchain-based supply chains would work by digitizing physical assets and recording them in a public ledger. This way, all participants in a decentralized supply chain network can track the state of a product, as well as all of its previous states and modifications.
For example, Starbucks can create a decentralized supply chain that tracks the production lines for coffee beans. On that network, we can view at what point farmers in Brazil have processed the coffee beans and have sent it outside of the country. Next, we can track when the shipment was sent, what quantity it contained, and when it arrived. This could be perfected to the point where a user, upon buying a cup of coffee in Starbucks, can open an application, scan the QR code of the cup and find out where his drink came from.
The use cases for blockchains in supply chains are nearly endless. Almost any industry and sector can utilize the technology to work together on producing higher-quality goods.
While companies can use ‘basic’ blockchain networks similar to Bitcoin, they can also upgrade supply chains with other features. For example, they can adopt smart contracts and decentralized oracles as well to improve data flow, create self-executing contracts, connect off-chain with on-chain data, etc.
Internet of Things (IoT)
The world is becoming more and more interconnected through each day. In modern times, both retail users and industry giants replace critical infrastructure with IoT-based smart devices. While an individual may use IoT to turn his home into a smart house, a manufactory may decide to digitize its production process with smart appliances.
Enduser spending forecast on IOT solutions worldwide (in billion dollars)
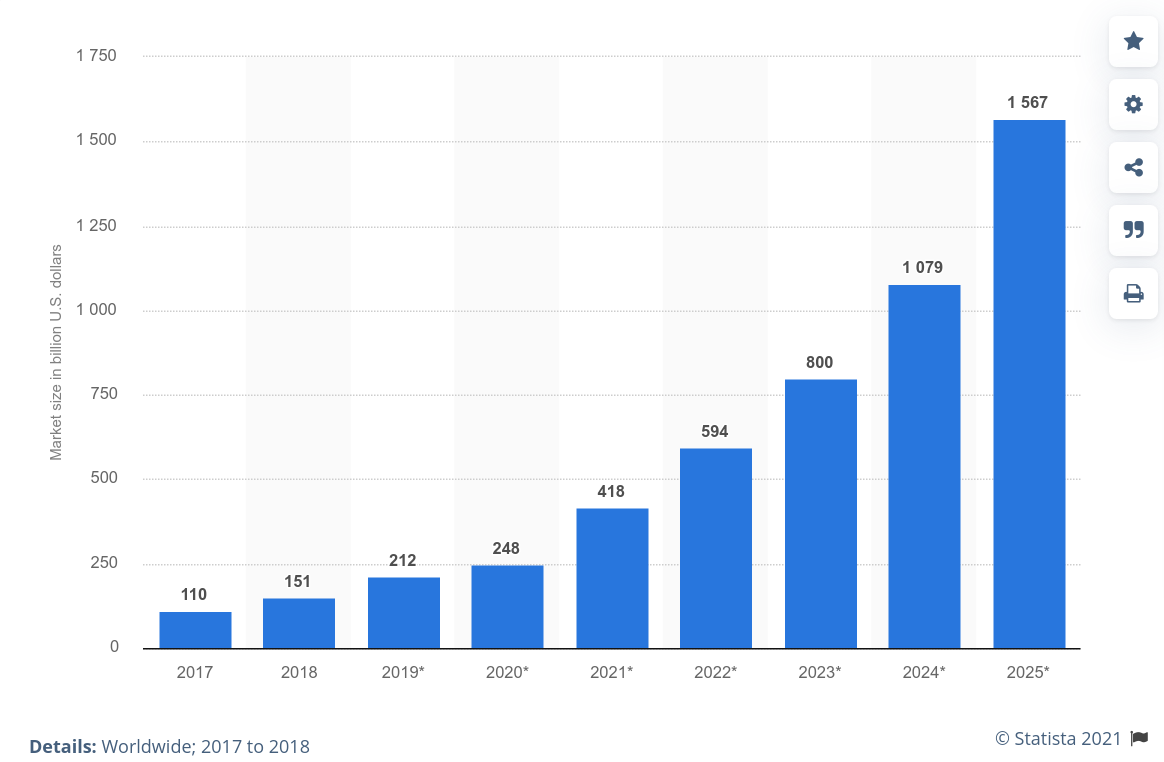 Source: statista.com
Source: statista.com
In the United States alone, spending on the IoT industry is predicted to reach $1.1 trillion by 2022. With the arrival of widespread new networks like 5G, we will see a boom of growth in the IoT market. However, a major problem is that future infrastructure is significantly susceptible to cyberattacks and data leaks.
To fix this problem, institutions all over the world are looking to adopt blockchain networks. How does decentralized technology exactly help in this case? Cryptographic encryption prevents malicious actors from taking control of a system. Moreover, blockchain helps with accessibility and usability for data transfers.
Here, we can also implement timestamping. For example, if a homeowner seeks to rent his smart house he can create a digital key that tracks who accessed his home and when. This removes any need for delivering physical keys. Furthermore, it ensures that the smart house is only available for a certain period and that the other person does not have access after it ends.
Content timestamping
Important legal and non-legal documents are definitely the most important use case for blockchain-based timestamping. Blockchain technology can be used to record, track, and authenticate the creation and modification times of documents. This is very important as physical and even modern digital documents are easy to manipulate and copy.
Users can replace modern notary services with a simple to use timestamping platform to ensure the ownership of their work. And all of this can be publicly and securely processed through a digital platform without the help of an intermediary.
All of this is done privately as well. You can offer proof of ownership at a certain time and date without revealing the content of your document. The same applies to the authenticity and integrity of the paper.
Users can timestamp any kind of digital media format. These formats include PDF, TXT, DOC, JPG, PNG, spreadsheets, drawings, etc. For example, artists can verify their ownership over drawings, books, literature, photos, and other artworks. An estate owner could prove in court his ownership over a certain home or verify at what time he purchased the place.
Another example of timestamping documents is the freelancing industry. If a client hired a freelancer to create a logo, he could request a proof of ownership via a timestamp. By doing so, the client can verify that the hired freelancer is the original creator of the delivered work. Similarly, a freelancer can timestamp his documents to make sure that they cannot be stolen or edited by others. The same holds true for any creator in any kind of industry in the world.
Academic researchers could also profit from timestamping. Similar to the previous examples, they can prove their ownership of a patent or paper without using a 3rd-party. However, they can also benefit from being able to search for other people’s work at one single point. There is no need to search for papers on hundreds of libraries and platforms. Users could simply discover the works of an author under one public blockchain network.
Likewise, tracking documents and their certification is often a headache as they are certified by numerous regulatory bodies, institutions, and platforms. Therefore, tracking and researching documents becomes a complex problem that takes too much of your time. To resolve this, we could use a blockchain explorer to research this information instead of opening dozens of websites to individually search the documents we need.
Social & Governance
Last but not least, we have governance and our very own social life. Both are equally important and both contain similar problems that still persist in 2020. With all aspects of life becoming digital, we must overcome these obstacles by utilizing technologies that actually make a difference. In the case of governance, we must make sure that our vote mattered and that it was not used to place someone else in power.
Apart from voting, we must also protect our identity. Today, it is easy to act like someone else without anyone knowing it. Criminals often steal identities and personal data to perform malicious acts and in most cases, there is no real mechanism to prevent that before any harm was done.
To prevent fake votes and stolen identities from ever happening again, governments and institutions must adopt blockchain technology. To explain how this weird mix would work, we will showcase how information can remain private and decentralized at the same time.
Voting
Just like everything else in the world, voting is also being digitalized in numerous countries. To make the process secure and transparent, it is extremely important to use the right technology. Blockchain networks can fight against manipulation and voter fraud, as well as track the number of eligible voters.
Since modern digital voting systems are often susceptible to manipulation and hacks, it would be useful to adopt blockchain technology. On that account, the election process could be fully determined by voters who reach consensus on a public or private network. With timestamps, a citizen could also have proof that he voted during the last elections, for example, and that his vote was not manipulated.
Apart from voting in elections, digital voting could also be used in other areas. A company could potentially introduce a governance mode for shareholders, who decide in which way the firm would go. This can be applied to any hierarchical system where a democratic consensus must be reached. To fight voting manipulation or prevent certain individuals from seizing power, we can utilize blockchain technology.
Identity and KYC
Passports, birth certificates, ID documents, and other forms of identification are lost or stolen every year. There is yet no system that can combat this problem to a degree that it is impossible to lose ownership over your identity or have someone else steal it. However, blockchain technology can yet again offer a viable solution.
Identities can be digitized and converted into an online format that is immutable. If an identity is already submitted to the network with a certain ID number, no one could copy or change it. Similarly, a person could show his ownership over the document by showing a proof of existence. Apart from administrative purposes, this could also be utilized in cases where companies and platforms request KYC information.
Know Your Customer (KYC) is a guideline in financial services that require trading platforms and exchanges to own a user’s identification documents. These documents are then sent to regulatory bodies in cases where the user is suspected to conduct illegal actions. A problem with current KYC software that exchanges use is that they are susceptible to cyberattacks. Over the past year, we saw a rise in data leaks where hackers got access to thousands of identities.
To prevent this from happening, regulatory exchanges could develop a permissioned blockchain where only financial entities and regulators have access to KYC information. Since the network is cryptographically encrypted and private, it is impossible for a hacker to reach the information. Such an integration would severely lower the cases of stolen or misused identities.
What is OriginStamp?
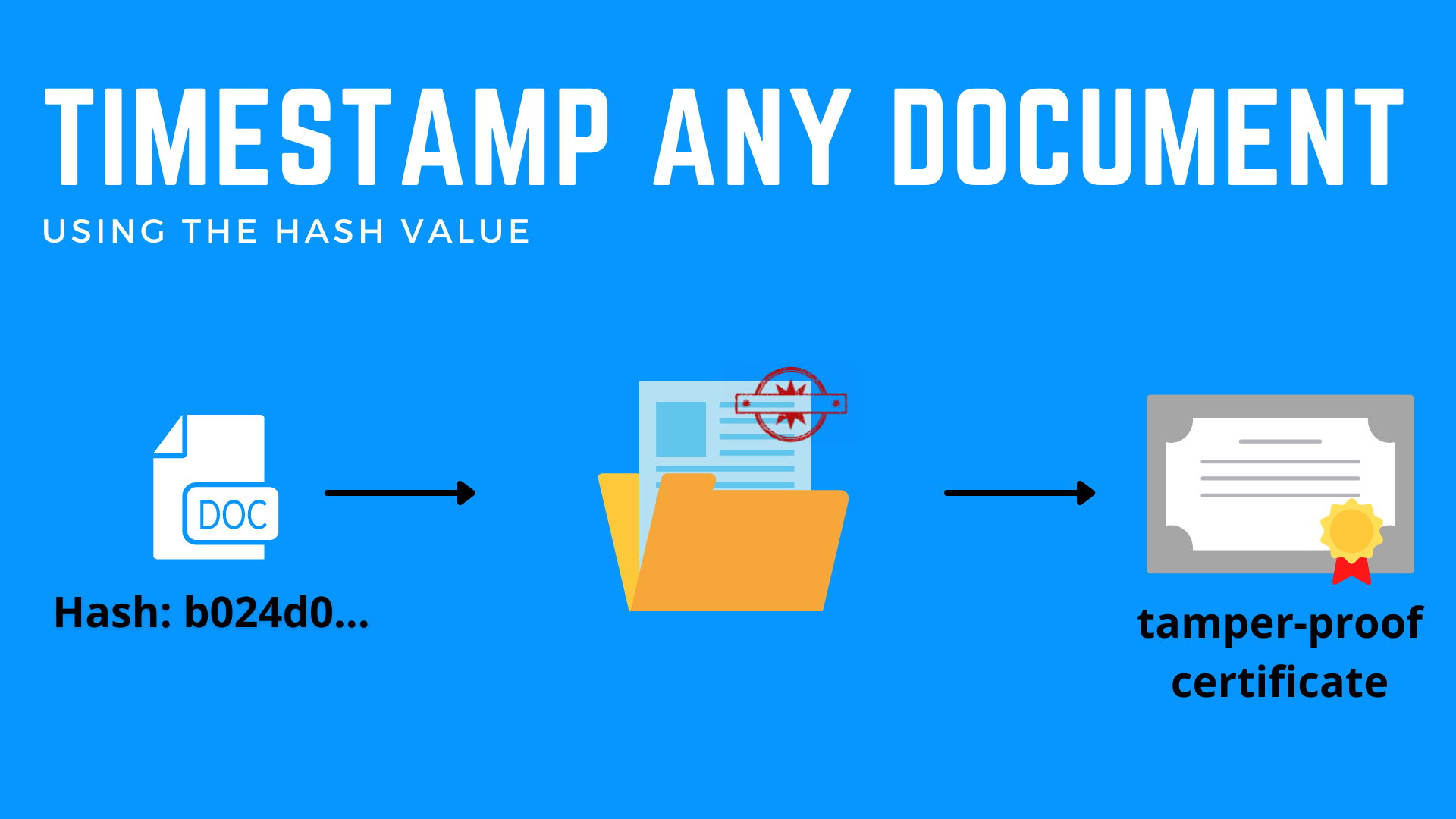
OriginStamp is an internet platform that provides trusted timestamping based on decentralized blockchain technology. Users can anonymously create tamper-proof timestamps for all kinds of digital content. With the service, you can create, retrieve, and verify any timestamp recorded on the blockchain network.
Researchers, students, authors, artists, journalists, businessmen, and others can use OriginStamp for free to authenticate the validity of their data. Free users can utilize either the platform's API or dashboard with a limited amount of monthly credits. For those who may have to timestamp documents on a daily basis, they can apply for a variety of paid plans.
At the time of writing, OriginStamp supports four blockchain networks, including Bitcoin, Ethereum, Aion, and Südkurier. However, these networks vary by their timestamping interval. For example, Bitcoin has a one-day interval while Ethereum and Aion offer a 1 hour and 10 minutes interval respectively. On the other hand, Südkurier is a media blockchain that allows users to create timestamps on average every 24 hours.
To better explain how timestamping works on OriginStamp, we will showcase the platform’s mechanism and capabilities in the next section.
How does blockchain-based timestamping work at OriginStamp?
The process of timestamping documents at OriginStamp is quite simple. The model relies on traditional decentralized blockchain technology and therefore uses concepts such as hashing, Mercle Trees, private keys, etc. In this section, we will explain the process of generating timestamps by using the Bitcoin blockchain.
The file whose existence and modification time we need to timestamp must be first made available in the proper digital format. For example, this can be anything starting from a PDF scan, a text file, a digital photo, a video, etc.
To submit the timestamp for this digital format to a blockchain network like Bitcoin, we must first create a cryptographic hash of that file. The OriginStamp platform can create such a hash locally on its client. To ensure the confidentiality of a file, the client will only send the SHA-256-based hash as it is impossible to determine the input of such a file. Additionally, we save on the file size as SHA-256 hashing is limited to 32 bytes. Therefore, we make sure that even larger files produce a relatively small fingerprint.
After producing both the fingerprint and timestamp of the digital document, we have to submit it to the blockchain network. However, we would clog up the Bitcoin network if we were to send the data immediately after creating it. To prevent that, OriginStamp creates a single transaction for all of the hashes submitted in a 24-hour period. This is made possible with the help a Merkle Tree, which allows hashes to be efficiently combined. More than network congestion, this process also helps with increasing the economic efficiency of submitting timestamps.
Submitting individual hashes on your own would be highly costly, especially if you were to do so at a high frequency. A single Bitcoin transaction fee costs anywhere between $1 to $3 at the time of writing. In periods of high network congestion, these fees can reach astronomical levels. For example, a single transaction cost $55 at one point in December 2017. Therefore, it would be highly inefficient to send hashes on your own and especially to submit them individually. OriginStamp can simply process a high number of requests and send them in one go every 24 hours to lower the costs not only of the user but of the overall blockchain network as well.
To finally create the timestamps, OriginStamp uses the root hash of the Merkle Tree as a private key to create an uncompressed Bitcoin address to which the data will be sent in the form of a dust payment. Considering that it is highly unlikely that the final address was already used for a previous payment, we can acknowledge the time of the addresses’ first payment as the time of the newly created timestamp. This way, we can use this as proof of existence for the private key at the time. Finally, after the new transaction is confirmed by miners after six blocks, the process will be finally completed.
A step-by-step guide for using OriginStamp
The OriginStamp platform is easy to use and requires no technical knowledge at all. Since the service is free, you can try it out right now to test the system’s capabilities. If you already have a document that you wish to permanently record on a blockchain network, now would be a perfect time!
To start, visit the official OriginStamp website and click on ‘Start Now.’ You will be redirected to the registration page where you are only required to input a valid email address and a secure password. After registering, make sure to verify your account by going to your email service and finding the latest email received by OriginStamp. Click on the verification link and the registration process is completed. You can now finally log in.
The OriginStamp Dashboard features four different tabs, including Overview, My Timestamps, Integrations, and Automate & API. As you can see, these names are pretty straightforward and already explain their functions. Before we explain the rest of the platform, we will start by creating our very first timestamp.
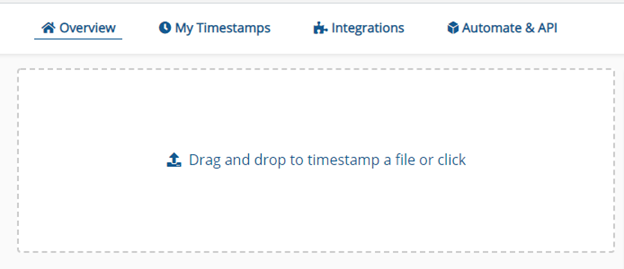
For the purpose of this guide, we created a simple text file (.txt) which we will upload to OriginStamp in the ‘Overview’ section. Due to its relatively small size, it only took a few seconds for the file to upload. Moreover, we have instantly received the hash of the file and are already prepared to submit a timestamp request which will later be sent to the blockchain network.
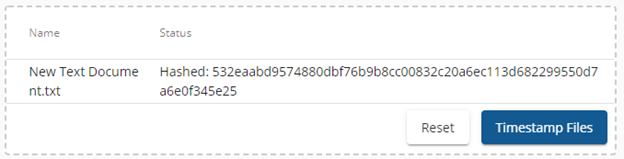
After clicking on ‘Timestamp Files,’ the file’s hash has been submitted. As we previously explained, OriginStamp submits a set of hashes every 24 hours when using the Bitcoin blockchain network. If we wish to timestamp another document or file, we can do so.
To verify the state of the file, we can head over to the ‘My Timestamps’ section.
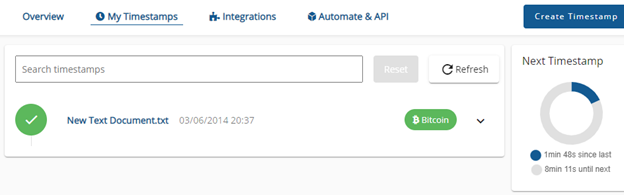
Here, we see at what date the document was successfully timestamped and to which network. If we wish, we can also download a timestamp certificate of this file for verification purposes. Within the document, we receive the name of the file, its hash, transaction, and even private key.
The downloaded certificate also contains steps for the purpose of verifying our file’s timestamp. We can determine the SHA-256 of our original file, validate its proof, determine the private key, determine the Bitcoin address, and of course, check the transaction via a block explorer. All of these steps are relatively easy to follow and only take a few minutes to complete.
As we mentioned, OriginStamp offers two more features on its platform. By heading to the ‘Integrations’ sector, we can combine OriginStamp with a number of other apps and platforms. For example, we can integrate our OriginStamp account on Dropbox, a website for storing, uploading, and downloading files.
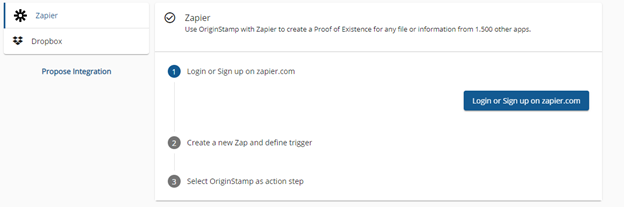
You can also utilize Zapier, a platform tool that connects your OriginStamp account with more than 1,500 applications, including email services like Gmail and Outlook.
Last but not least, you can also automate timestamping and integrate it into your own apps and platforms by using the REST API. API clients for Python, Java, and C# are available. You can learn more about automated blockchain-based timestamping by visiting our documentation page.
Stay informed with the latest insights in Crypto, Blockchain, and Cyber-Security! Subscribe to our newsletter now to receive exclusive updates, expert analyses, and current developments directly to your inbox. Don't miss the opportunity to expand your knowledge and stay up-to-date.
Love what you're reading? Subscribe for top stories in Crypto, Blockchain, and Cyber-Security. Stay informed with exclusive updates.
Please note that the Content may have been generated with the Help of AI. The editorial content of OriginStamp AG does not constitute a recommendation for investment or purchase advice. In principle, an investment can also lead to a total loss. Therefore, please seek advice before making an investment decision.

Defensive Publication as an Intellectual Property Protection Method
Protecting intellectual property is essential for every business. Read what a defensive publication is and how it can protect intellectual property from others?

Top Blockchain Startups to Watch in 2021 - Innovative Use of Blockchain Technology
Discover the top blockchain startups of 2021 that are innovatively using blockchain technology to reshape various industries.

Importance of Security, Traceability, and Immutability at OriginStamp
Understand the significance of Security, Traceability, and Immutability at OriginStamp with blockchain technology. Learn how these features enhance document validation and data integrity.
Protect your documents
Your gateway to unforgeable data. Imprint the authenticity of your information with our blockchain timestamp