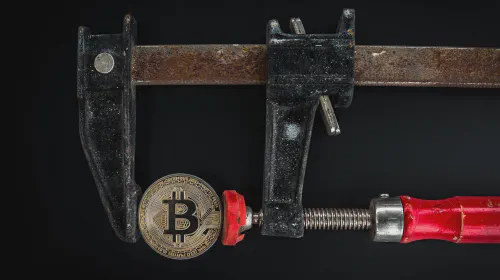
Why Do Hackers Use Bitcoin?
Salomon Kisters
Nov 9, 2022This post may contain affiliate links. If you use these links to buy something we may earn a commission. Thanks!
Because of its decentralized and anonymous nature, Bitcoin is the preferred currency of hackers and scammers all over the world. Furthermore, the lack of a regulatory framework in this sector makes it appealing to scammers.
For the past few years, Bitcoin and cryptocurrencies have been the hottest topics in the tech world. Blockchain technology, which has only been around for a little over a decade, has made waves in the world of fintech. And decentralized finance is causing us to reconsider our current financial structure.
However, despite all of the ways this technology can improve our lives, it does have some drawbacks. The most visible is a virtual currency, which is used by hackers for ransom and scams.
What is Bitcoin?
Bitcoin is a cryptocurrency based on an open-sourced decentralized blockchain ledger with a limited supply of 21 million coins. It was created to facilitate peer-to-peer monetary transactions between any two individuals, parties, or businesses without involving any third party for verification. Compare it with our traditional financial system which is dependent on centralized banks to validate and process transactions.
Bitcoin was created in 2009 by a developer or group of developers, pseudonymously known as Satoshi Nakamoto. At the time one Bitcoin token was valued just a fraction of a dollar. Today it is the biggest cryptocurrency with a market capitalization of around $370 million. At the time of writing this article (November 2022), one Bitcoin token is worth over $19,000.
How does Bitcoin Work?
If Bitcoin is not controlled by any centralized body and no bank validates the transaction, how does the network maintain its authenticity and stop individuals from exploiting the system? The answer is the consensus mechanism.
Bitcoin uses a consensus algorithm called the proof-of-work mechanism to authenticate and record transactions on its decentralized ledger. In this consensus mechanism, thousands of individual nodes around the globe participate to maintain the network functioning. These nodes are called miners.
Miners compete against each other to win the chance to record and add a new block to the blockchain. Every node around the network tries to solve a highly complex mathematical problem simultaneously, and the node to solve it first is elected by the blockchain to process transactions. The process of solving the mathematical problem involves a lot of computational power and a massive energy supply.
The elected node then records the newly validated transactions on an empty block. After the block is filled, it is added to the blockchain and the validator node is rewarded with some newly minted BTC tokens as a reward for participation.
Currently, there are over 100k Bitcoin nodes around the world, making it one of the most decentralized cryptocurrencies. The mining reward is 6.25 BTC as of 2022. However, this reward is reduced to half every 4 years. The total number of Bitcoin tokens that will ever be available is 21 million. After that, the validators will stop getting any mining rewards.
What Makes Bitcoin Appealing to Hackers?
The following are the biggest factors that make Bitcoin a preferable currency for hackers to carry out ransoms and scams.
Decentralized
The most prominent factor which leads hackers to use Bitcoin is its decentralized nature. Unlike our traditional fiat currencies, there are no centralized entities, such as banks or governments, monitoring and controlling the monetary network in the case of Bitcoin.
Instead, the blockchain is controlled by the network participants themselves and no one has a greater say than the rest. This reassures hackers since no one can restrict their wallets or stop their transactions from processing.
Fast Transactions
Bitcoin is infamous in the cryptocurrency space for its slow transaction speed. It can only validate 6-7 transactions per second. Meanwhile, other projects like Solana and Avalanche can process thousands of transactions in the same period.
However, despite these incredibly fast crypto projects, transactions made through the Bitcoin blockchain are still much quicker than transferring money through most banks around the world. Moreover, you must also note that Bitcoin is not the only cryptocurrency used for scams. Many hackers also use other crypto coins such as Monero and Litecoin.
Anonymity
Recall the procedure you had to go through while opening an account in your local bank. It involves an awful lot of steps and various identity verification processes. You have to submit several official documents. Only after a lengthy procedure do you get to use your bank account for sending and receiving money.
When it comes to the world of cryptocurrency, the case is the opposite. To set up a Bitcoin or crypto wallet, all you need to do is download a chrome extension and set up a password to access your wallet. This allows hackers to stay under the radar.
Lack of Regulations
Cryptocurrency is often regarded as the “Wild West” due to the lack of government regulations around the technology. Being such a novel innovation, the regular laws of commodities and securities, such as stocks, do not apply to cryptocurrencies.
Most governments around the world are still trying to understand how this virtual currency works and which areas require a regulatory framework. Hence, federal agencies are unable to carry out any operations to effectively prevent such hacks and ransom attacks.
How do Hackers Use Stolen Bitcoin?
As per Chainalysis’s mid-year report, hackers stole nearly $2 billion worth of Bitcoin and other cryptocurrencies during the first half of 2022. If they are stealing such large sums of digital currencies, a common question arises: where and how are they spending this amount?
Exchanges
The most straightforward way to use Bitcoin and cryptocurrencies is to flip them for fiat currency through a centralized exchange. However, almost every exchange these days follows Know Your Customer (KYC) policies. As a result, to use their services users have to verify their identity and submit official documents.
According to Chainalysis analysis, almost 80% of the Bitcoin stolen was transferred only to five crypto exchanges. This shows that there are still a few exchanges that allow hackers to maintain their anonymity and sell stolen funds.
Dark Web
Many hackers use stolen Bitcoin to pay for illegal services on the dark web. A lot of drug dealers and other illegal vendors in the realm of the dark web accept only cryptocurrencies as payment methods. The most used cryptocurrencies for this purpose are Bitcoin, Ethereum, and Monero. Hence, it makes total sense for hackers to spend the robbed crypto funds in the online black market.
Peer-to-Peer Transactions
Another popular way of converting your Bitcoin into a fiat currency is through peer-to-peer (P2P) transactions. In P2P transactions, instead of using an exchange service to sell your cryptocurrency, you sell them directly to an individual.
To make it even harder to trace the stolen funds, they divide the total amount into small portions and transfer them to several addresses. This technique is called a mixer and gives hackers an added layer of disguise.
So Can We Track These Hackers?
While hackers learn new ways to utilize cryptocurrencies to carry out illegal activities and ransom attacks, federal organizations and agencies, such as the FBI and SEC, are also upgrading. With the widespread adoption, quickly growing adoption, and increasing numbers of crimes in the cryptocurrency space, these departments are forced to research and learn about this newly emerged sector thoroughly.
Many governments around the world have already started working on formulating a regulatory framework to ensure a safe and fair ecosystem for crypto users. Earlier this year, Joe Biden – president of the United States – passed the first-ever executive order to direct federal bodies to work on crypto regulations. Similarly, Dubai also issued its first-ever law for cryptocurrencies and virtual assets at around the same time.
Moreover, contrary to the common misconception, Bitcoin does not give you complete anonymity. Though you can create a digital wallet and carry out transactions without revealing your identity, the transactions can be easily tracked. Being an open-sourced network, anyone around the world can use tools like Blockchain Explorer to track the entire journey of any transaction. So, by monitoring the activity of a suspicious wallet, government officials can easily trace down thieves and hackers using cryptocurrencies.
With increasing jurisdictions exchanges are also forced to follow KYC policies and verify the identities of all their users. Almost every country around the globe requires crypto trading platforms to conform to a set of certain rules to get licensed permission to function in the region.
As a result of all this regulatory development, it is getting harder for hackers and scammers to get away by using cryptocurrencies. With time, as this landscape further matures, we will see a significant decrease in the number of crimes in the cryptocurrency space.
Origin Stamp is a committed team of software and blockchain experts who have been working in the space since 2011. We develop mobile apps and enterprise software and provide secure turnkey blockchain solutions for businesses. Contact us today for a free consultation.
Stay informed with the latest insights in Crypto, Blockchain, and Cyber-Security! Subscribe to our newsletter now to receive exclusive updates, expert analyses, and current developments directly to your inbox. Don't miss the opportunity to expand your knowledge and stay up-to-date.
Love what you're reading? Subscribe for top stories in Crypto, Blockchain, and Cyber-Security. Stay informed with exclusive updates.
Please note that the Content may have been generated with the Help of AI. The editorial content of OriginStamp AG does not constitute a recommendation for investment or purchase advice. In principle, an investment can also lead to a total loss. Therefore, please seek advice before making an investment decision.
Can The Blockchain Be Hacked Or Attacked?
Blockchain technology and cryptocurrencies have seen a massive surge in popularity. Can they be hacked?

Here Is Why Bitcoin Transactions Take So Long
Why do Bitcoin transactions take so long? Here are the reasons and methods to speed them up.

How Blockchain Technology Enhances Provenance
Blockchain technology enhances provenance by providing a secure and immutable tracking mechanism for data, ensuring authenticity and trust in various industries.
Protect your documents
Your gateway to unforgeable data. Imprint the authenticity of your information with our blockchain timestamp